Critical Threat Intelligence & Advisory Summaries
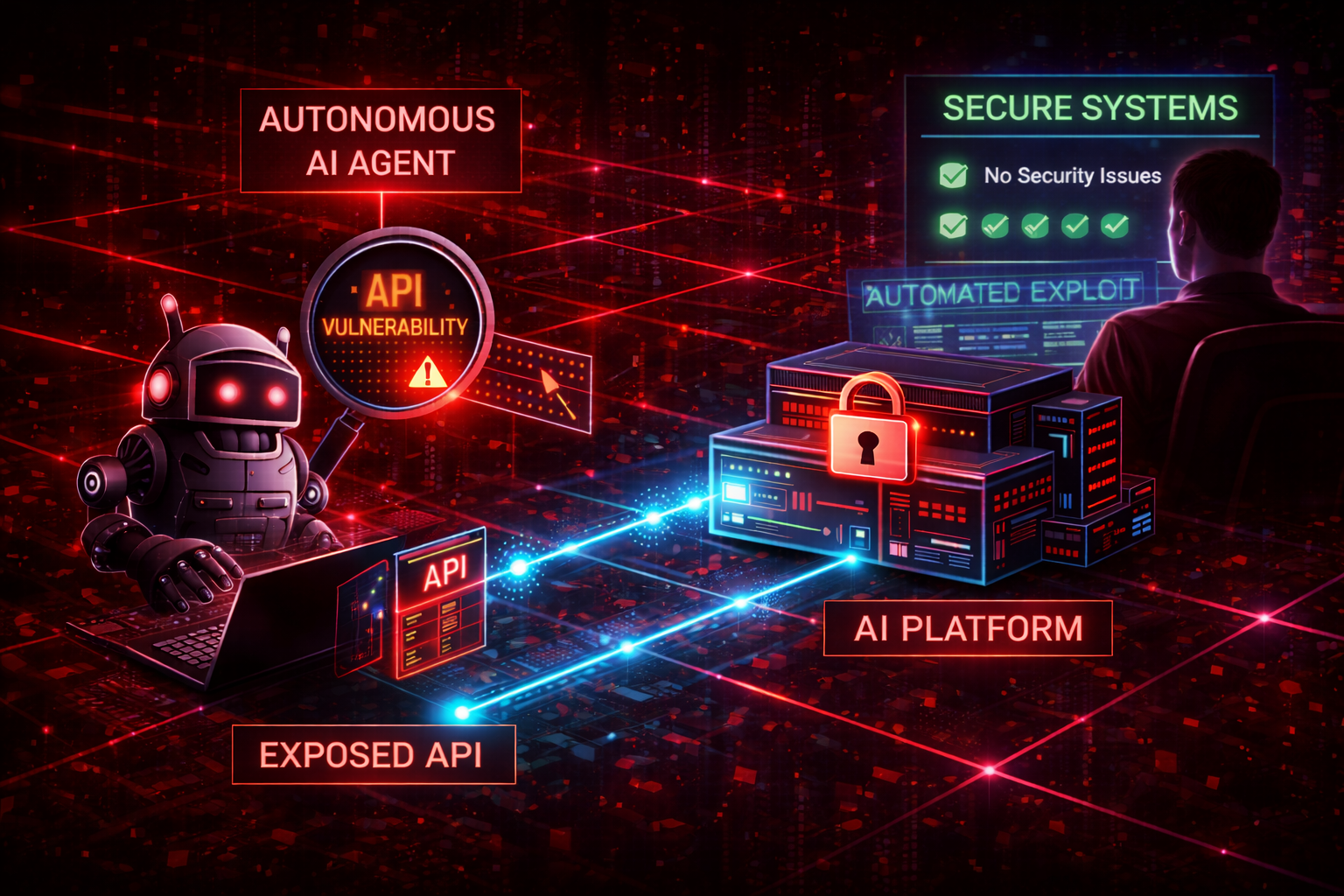
McKinsey’s reported AI chatbot breach highlights a growing enterprise risk: insecure deployment of generative AI platforms. This Operational Failure Analysis examines how identity governance gaps, shadow AI adoption, and weak platform controls can expose sensitive enterprise data.
With 59,000+ vulnerabilities projected in 2026, organizations must rethink patching. This article explains why exposure-based prioritization is critical to reducing real-world cyber risk.
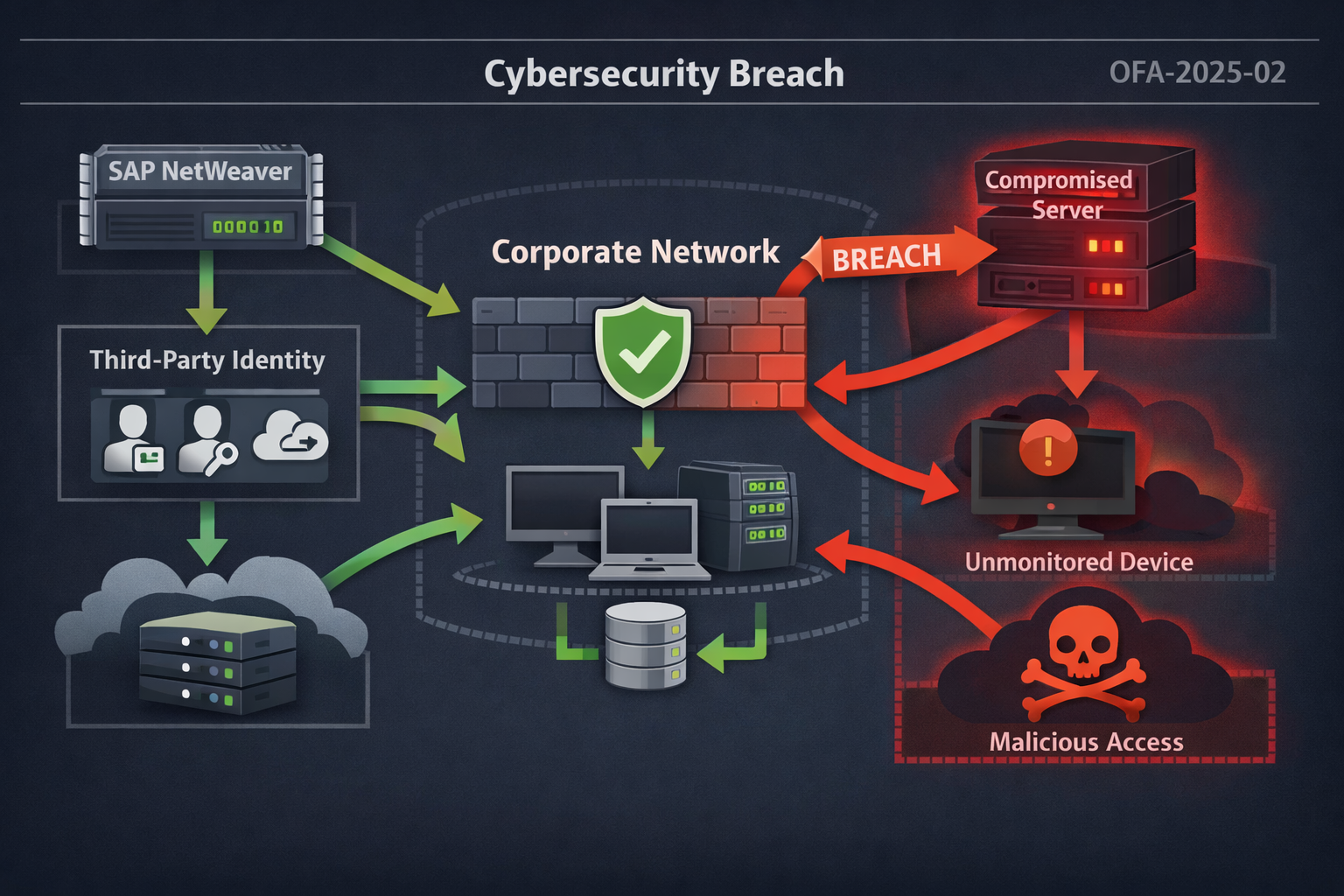
JLR breach analysis highlighting third-party identity exposure, KEV prioritization gaps, and lessons for operational threat intelligence teams.
Operational threat intelligence enables security teams to prioritize real-world risks through detection-focused monitoring and actionable insight. This guide addresses detection challenges, attack chain visibility, and defensive strategies for SOCs confronting identity-based threats, insider risk, and AI-enabled cyber campaigns.
AI-driven impersonation attacks including deepfake video fraud, voice cloning scams, and synthetic job applicants are redefining enterprise cyber risk. This guide explains the threat landscape and how SOC teams can detect and mitigate AI-enabled identity attacks.