Critical Threat Intelligence & Advisory Summaries
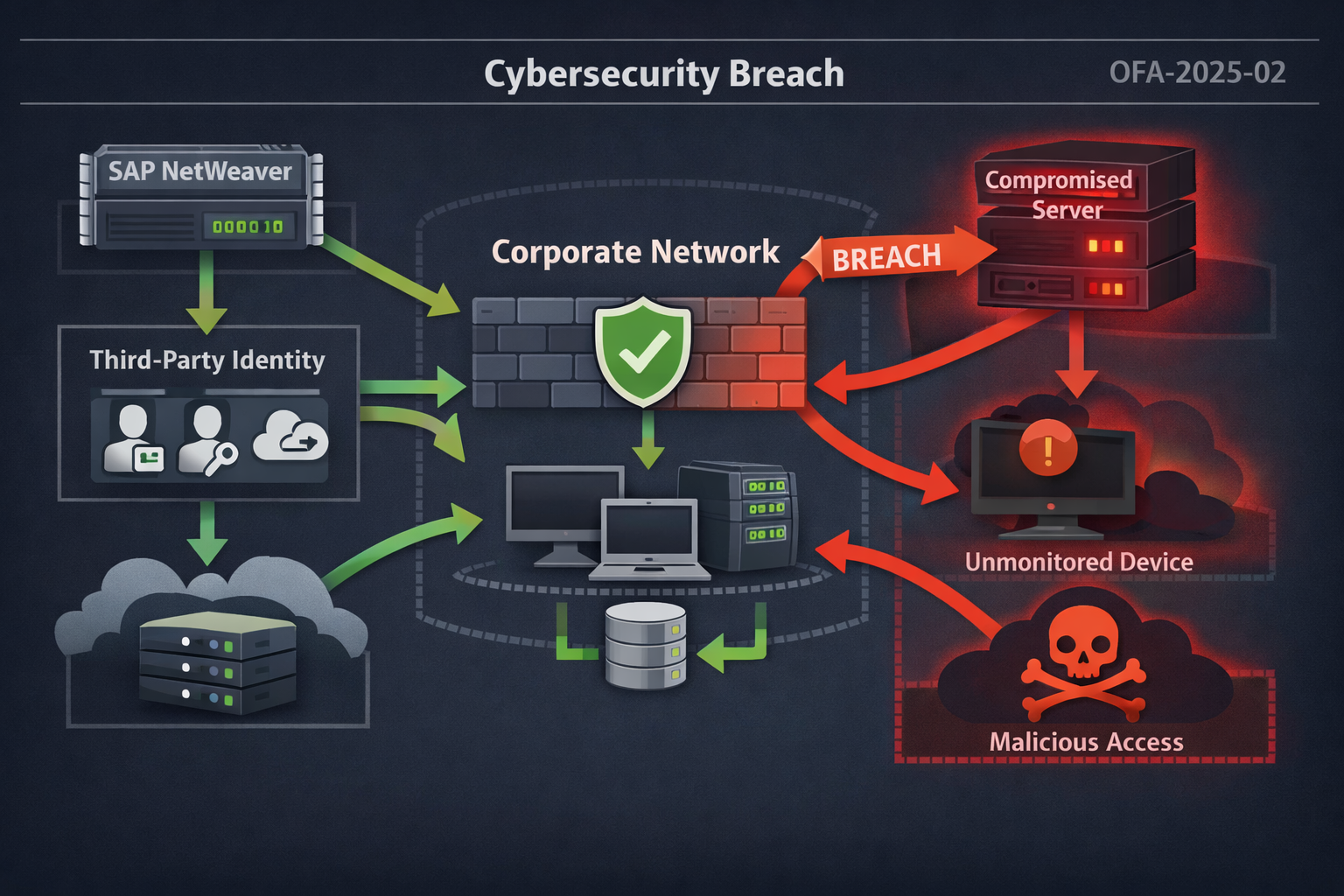
JLR breach analysis highlighting third-party identity exposure, KEV prioritization gaps, and lessons for operational threat intelligence teams.
Operational threat intelligence enables security teams to prioritize real-world risks through detection-focused monitoring and actionable insight. This guide addresses detection challenges, attack chain visibility, and defensive strategies for SOCs confronting identity-based threats, insider risk, and AI-enabled cyber campaigns.
HONG KONG — As real-time deepfake fraud losses surpass $200 million in early 2026, global enterprises are discovering that traditional "see-and-hear" verification protocols have become their greatest liability. This report analyzes the recent $25.6 million Arup heist and the UAE bank voice-clone incident to expose how "perfect compliance" with obsolete security models is enabling industrial-scale deception. Learn how to implement the 2026 Universal Control Framework to protect your organization's assets from increasingly sophisticated agentic AI attacks.
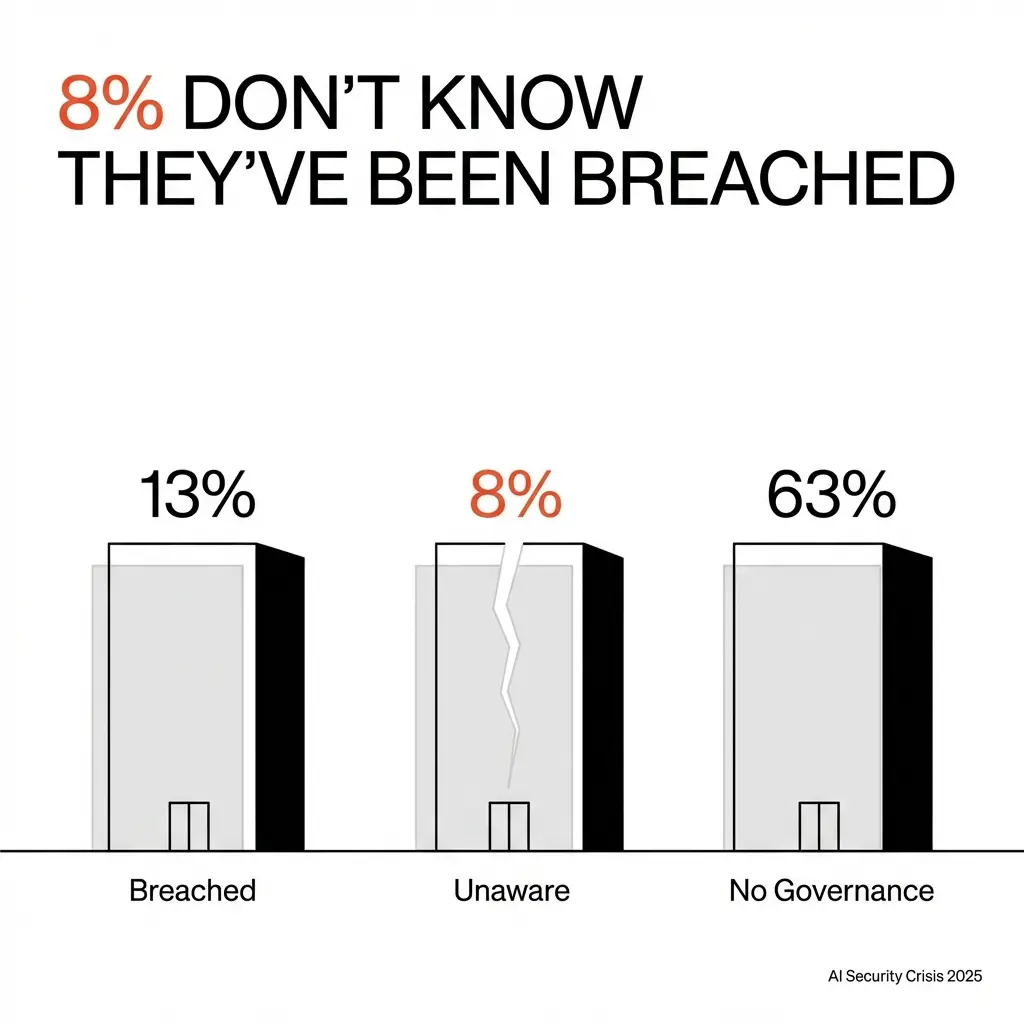
AI breaches aren’t coming through firewalls anymore, they’re happening through conversations. While organizations celebrate productivity gains, sensitive data is leaking through tools no one is tracking or governing. This isn’t a future risk, it’s already happening.
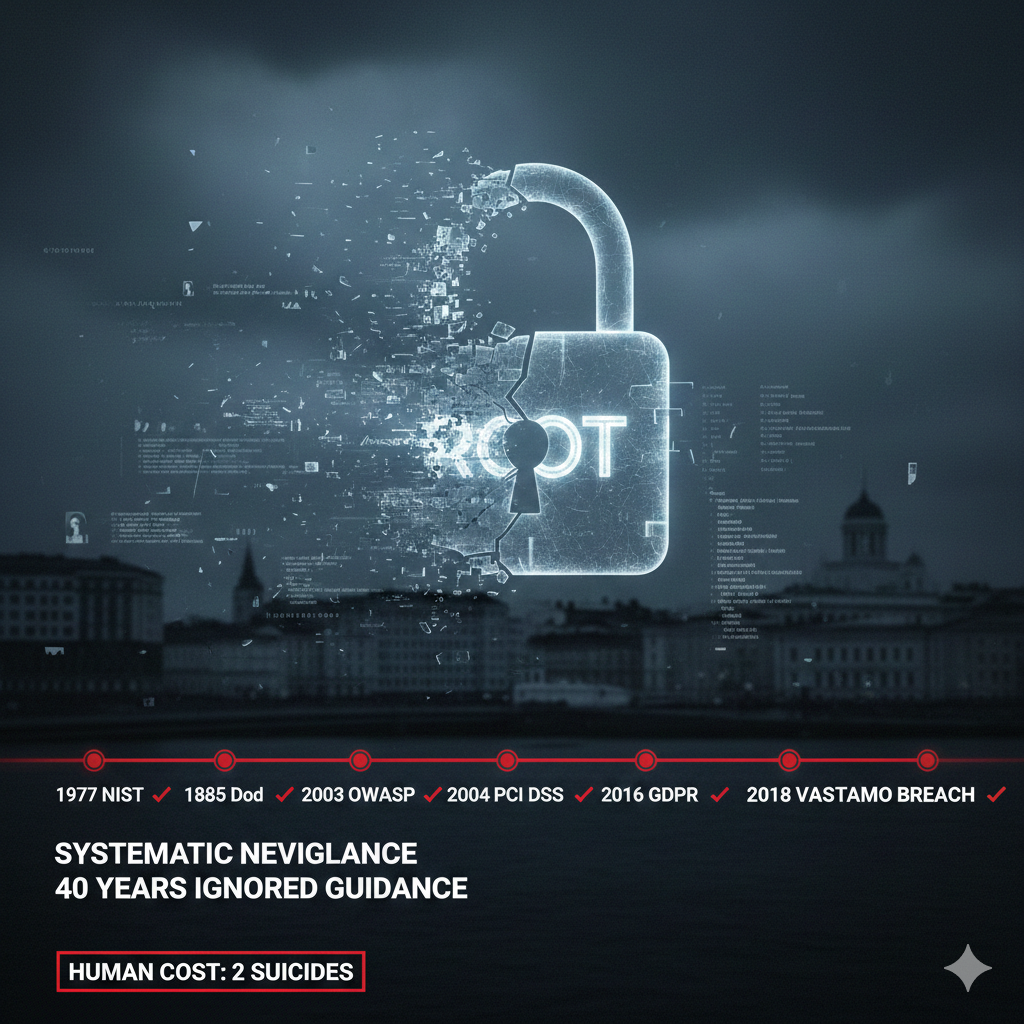
The Vastaamo breach exposed 33,000 Finnish psychotherapy patients to direct extortion, concealed it for 18 months, two people died by suicide. The deeper failure: 40 years of ignored security lessons.