Critical Threat Intelligence & Advisory Summaries

CitrixBleed to BlueHammer: Identity Governance Failure Repeats (OFA-2026-04-CXB)
Operational Failure Analysis: OFA-2026-04-CXB
As CISA's April 20 KEV additions targeting Cisco SD-WAN, JetBrains TeamCity, PaperCut, and others and address the ongoing BlueHammer situation where two related zero-days remain unpatched, a diagnostic question emerges: Are organizations repeating the core failure that enabled CitrixBleed?
CISA added eight vulnerabilities to the Known Exploited Vulnerabilities Catalog on April 20, 2026, with federal remediation deadlines set for May 4. The BlueHammer exploit (CVE-2026-33825) achieved SYSTEM-level privilege escalation through a race condition in Microsoft Defender's threat remediation engine, a time-of-check to time-of-use flaw that allows an attacker to redirect a privileged file write operation mid-flight using filesystem manipulation. Microsoft patched BlueHammer on April 14. Two related zero-day variants, RedSun and UnDefend, remain unpatched as of April 21. The three vulnerabilities were released in a 13-day window by a researcher who cited Microsoft's handling of the initial disclosure as the reason for going public without coordination, a dispute that has its own active news thread in the security community.
The broader April 2026 threat picture has also included sustained Fortinet FortiClient EMS exploitation: CISA added CVE-2026-35616 on April 6 and CVE-2026-21643 on April 13 two separate KEV entries for the same product family within two weeks, a pattern that directly illustrates the authentication infrastructure targeting theme at the heart of this analysis.
Security practitioners face the same operational test that Boeing, ICBC, and other CitrixBleed victims failed in late 2023: recognizing that patching software and eliminating persistence represent fundamentally different remediation activities. The MFA bypass mechanisms differ, CitrixBleed leaked session tokens through buffer over-reads; BlueHammer escalates privileges through Defender's remediation engine but the identity lifecycle enforcement gap remains identical.
CitrixBleed (CVE-2023-4966) remains the definitive case study for why session invalidation and authentication artifact management constitute the true "patch" for 2026 infrastructure. The following analysis reconstructs where control systems failed and what operators must verify within their own environments today.
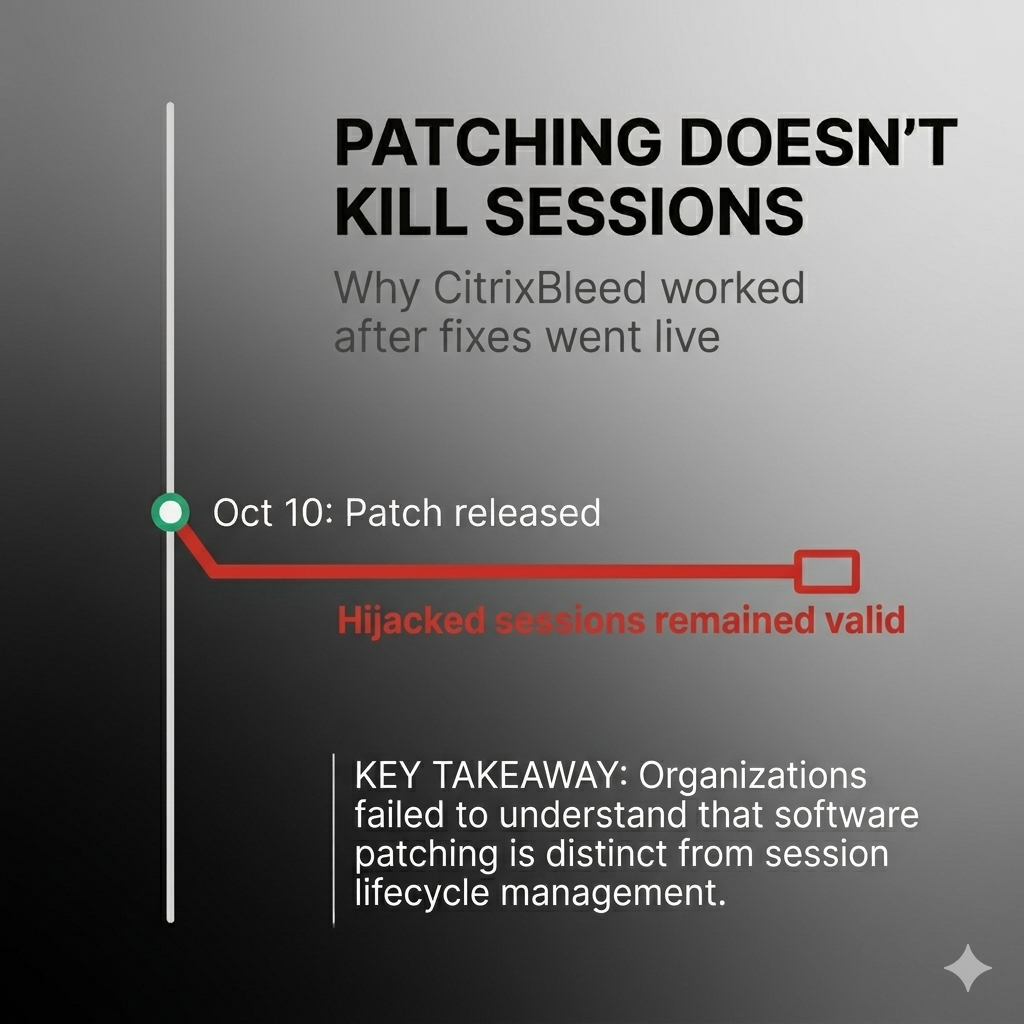
CVE-2023-4966 scored 9.4 on CVSS. Citrix released patches on October 10, 2023. Organizations deployed updates within their standard remediation windows. Attackers maintained access for weeks afterward.
The vulnerability allowed session token extraction from memory through a buffer over-read condition in NetScaler ADC and Gateway appliances. Organizations patched the software defect. They did not invalidate the compromised sessions. Multiple nation-state APT groups and ransomware affiliates exploited this gap between remediation and session lifecycle management.
This incident highlights a failure in Identity Governance. Specifically, the systemic inability to recognize that vulnerability remediation and authentication artifact invalidation represent distinct security operations.
The Breach Snapshot
Vulnerability: CVE-2023-4966 affecting Citrix NetScaler ADC and Gateway appliances
CVSS Score: 9.4 (Critical)
Attack Vector: Buffer over-read condition enabling session token leakage from appliance memory
Confirmed Exploitation: Late August 2023 through November 2023 (zero-day exploitation period plus post-patch persistence)
Affected Organizations: Government entities, technology firms, critical infrastructure operators, legal and professional services firms
Impact: Unauthorized access to enterprise networks, MFA bypass, persistent authenticated sessions enabling lateral movement and data access
Threat Actor Profile: Multiple nation-state APT groups tracked by Mandiant; ransomware affiliates including LockBit 3.0 and AlphV/BlackCat
Timeline of Signals
The defender's view reveals a 10-week window from initial exploitation to mass weaponization. Each phase created distinct detection and remediation opportunities.
Late August 2023 – Zero-Day Exploitation Begins Signal Available: None from vendor. Network anomaly detection possible through session behavior analysis. Defender Opportunity: Organizations with NetScaler access log monitoring could detect session tokens used from multiple source IP addresses simultaneously. Mandiant later confirmed it was conducting active investigations during this period where a threat actor was taking over user NetScaler sessions through means that were not yet understood.
October 10, 2023 – Citrix Releases Patches Signal Available: Vendor security bulletin published. No exploitation confirmed publicly at time of release. Defender Opportunity: Standard vulnerability management cycle initiated. Citrix explicitly recommended killing all active and persistent sessions following the update, providing specific CLI commands to do so. Most organizations patched without executing the session invalidation step.
October 17, 2023 – Citrix Updates Advisory / Mandiant Publishes Findings Signal Available: Vendor confirms active exploitation observed in the wild. Mandiant publishes its investigation findings, disclosing that zero-day exploitation had been occurring since late August and warning explicitly that patched devices could still be accessed via stolen session tokens. Defender Opportunity: Urgency escalation trigger. Seven-day window since patch release. Organizations that patched but did not invalidate sessions remained vulnerable through hijacked tokens.
October 18, 2023 – CISA Adds CVE-2023-4966 to KEV Catalog Signal Available: Federal mandate for remediation within 15 days (internet-facing) or 25 days (internal) under BOD 22-01. Defender Opportunity: Binding operational directive for federal agencies. De facto priority signal for private sector. SLA clock starts.
October 25, 2023 – Public Proof-of-Concept Released Signal Available: Assetnote publishes technical analysis with working exploit code demonstrating session token extraction. Defender Opportunity: 15-day window since patch release. Weaponization phase accelerates sharply. Organizations that had patched and invalidated sessions in this window avoided the mass exploitation phase. Those that had patched without session invalidation remained exposed.
Late October – November 2023 – Mass Exploitation Confirmed Signal Available: Mandiant, CISA, FBI, and vendor reporting confirms widespread active exploitation by multiple threat actor groups including LockBit 3.0 ransomware affiliates. Defender Opportunity: Incident response and forensic investigation phase. Detection focus shifts to compromise assessment.
Critical Timeline Gap: Six-plus weeks of zero-day exploitation before patch availability. Fifteen days between patch release and public PoC. Organizations had a defendable window. Most failed to execute the complete remediation sequence.
Exploit Chain Breakdown
Initial Access Attacker sends a crafted HTTP GET request with an oversized Host header to a vulnerable NetScaler ADC or Gateway endpoint. The request triggers a buffer over-read condition in the appliance's memory management. Session tokens from active authenticated user sessions leak in the HTTP response.
The vulnerability exists in specific endpoints that do not log requests to standard webserver logs. Mandiant confirmed that it was not aware of any configuration change that could force request logging for these endpoints. Organizations without upstream network visibility, WAF or network packet capture, have no forensic evidence of exploitation attempts from appliance logs alone.
Persistence Attacker obtains a valid session cookie issued post-authentication. The session cookie includes multi-factor authentication validation state. Attacker uses the stolen token to establish an authenticated session without requiring a username, password, or MFA device. Session remains valid until natural expiration or explicit invalidation. Patching the vulnerability does not revoke existing sessions. Attacker maintains access through a legitimate authentication artifact.
Privilege Escalation Attacker inherits the privilege level of the hijacked session. If the compromised session belongs to an administrative user, the attacker gains administrative access without any additional exploitation.
Lateral Movement Across multiple incident response engagements, Mandiant observed attackers using authenticated NetScaler access to pivot into internal networks, conducting network reconnaissance, credential theft, lateral movement via RDP, and deployment of remote monitoring and management tools.
Impact Confirmed impacts include unauthorized access to enterprise applications, data exfiltration, ransomware deployment via LockBit 3.0 affiliates, and persistent access maintained through valid authentication tokens even after vulnerability patching. Boeing Distribution Inc. confirmed via a joint CISA/FBI advisory that LockBit affiliates used CVE-2023-4966 for initial access. ICBC Financial Services was also linked to CitrixBleed exploitation by security researchers, with the connection subsequently corroborated by the US Treasury, though this attribution was not confirmed through the same official government advisory process as Boeing.
Where the Control System Broke
Discovery Failure
NetScaler appliances function as authentication gateways. Many organizations lack complete inventory of authentication infrastructure assets. The appliances sit at network perimeter but do not always appear in standard IT asset management systems.
Organizations that did not know they operated vulnerable NetScaler instances could not patch. Discovery failure represents the first control breakdown.
Identity Governance Failure (Primary Breakdown)
Organizations treated vulnerability remediation as complete after patch deployment. Citrix explicitly stated in its October 10 advisory, and reiterated in follow-up guidance, that organizations should kill all active and persistent sessions following the update providing specific CLI commands for doing so.
Most organizations did not execute this step.
The failure reveals a fundamental misunderstanding of authentication architecture. Session tokens represent cryptographic proof of completed authentication. Once issued, tokens remain valid independent of the authentication system's security state. Patching prevents new token leakage. It does not invalidate tokens already compromised. Attackers using hijacked tokens bypass all authentication controls including MFA. The system cannot distinguish between legitimate user activity and attacker activity using valid tokens.
This represents a systemic identity governance gap. Organizations lack operational procedures for session lifecycle management during security events. Password resets, MFA enforcement, and software patching do not address authentication artifact persistence.
Prioritization Failure
CVE-2023-4966 entered CISA's Known Exploited Vulnerabilities Catalog on October 18, 2023. Federal agencies faced binding 15-day remediation requirements under BOD 22-01. The vulnerability received a CVSS score of 9.4. Public proof-of-concept code became available October 25. EPSS scoring would have reflected elevated exploitation probability following KEV inclusion and PoC release.
According to FIRST.org's published EPSS model data, organizations using a CVSS 7+ remediation strategy face 57.4% effort at 3.96% efficiency meaning the overwhelming majority of patching work is spent on vulnerabilities that are never actually exploited. Organizations using an EPSS threshold of 0.1 or above achieve 65.2% efficiency at 2.7% effort against the same vulnerability population. This represents a significant improvement in prioritization accuracy and suggests that teams relying solely on severity-based scoring may be directing resources away from actively exploited threats toward lower-risk work.
Segmentation Failure
NetScaler appliances provide authenticated access to internal applications and networks. Compromise of the authentication gateway enables lateral movement into trusted network segments. Organizations with network segmentation between authentication infrastructure and internal resources could limit attacker movement, though segmentation alone cannot prevent authorized access abuse through hijacked sessions, the gateway's function requires connectivity to protected resources.
Exploitation Intelligence Context
EPSS Percentile: Following KEV inclusion and public PoC release, CVE-2023-4966 would score in top exploitation probability percentiles. EPSS scores update daily based on exploitation signals.
KEV Inclusion: October 18, 2023 (eight days after patch release)
Known Exploitation Campaigns:
• Multiple nation-state APT groups tracked by Mandiant as exploiting CVE-2023-4966 during the zero-day period (late August through October 2023), targeting government, technology, and professional services organizations for espionage. Mandiant tracked these as distinct clusters of activity; specific attribution designations from Mandiant's threat intelligence research are drawn from non-public incident response reporting.
• LockBit 3.0 ransomware affiliates confirmed via joint CISA/FBI advisory, with Boeing voluntarily sharing TTPs
• AlphV/BlackCat ransomware affiliates reported across multiple security vendor investigations in the November 2023 campaign period
• Multiple financially motivated threat actors operating opportunistically following the October 25 public PoC release
Time to Exploit (TTE): Zero-day exploitation began late August 2023, six-plus weeks before patch availability. Post-patch exploitation continued through hijacked session persistence. Public PoC availability accelerated mass exploitation 15 days after patch release.
Exploitation Complexity: Moderate. Requires HTTP request crafting to the vulnerable endpoint. Public PoC reduced the technical barrier significantly following October 25 release.
Detection Difficulty: High. Exploitation leaves no webserver logs on the NetScaler appliance. Detection requires upstream network monitoring (WAF, packet capture) or behavioral analysis of session token usage patterns. Mandiant identified two primary detection signals: sessions accessed from a mismatched or suspicious source IP address versus the original client IP recorded at session creation, and multiple accounts accessed from the same source IP address within a short timeframe. Geographic impossibility, the same token used from widely separated locations within minutes represents a high-fidelity indicator of session hijacking.
What Would Have Prevented This
Tactical (48-Hour Actions)
1. Session Invalidation Post-Patch Execute vendor-recommended session reset following any authentication infrastructure update. Citrix published specific CLI commands for killing all active and persistent sessions. Treat session lifecycle management as a mandatory remediation step, not optional guidance.
2. Upstream Network Monitoring Deploy WAF or network packet capture for authentication gateway traffic. NetScaler appliances do not log requests to the vulnerable endpoint. Organizations without network-level visibility have no forensic evidence of exploitation from appliance logs alone.
3. Session Behavior Monitoring Alert on session tokens used from multiple source IP addresses within impossible timeframes. Mismatched client and source IP fields in NetScaler connection logs, and multiple accounts accessed from the same external IP in a short window, represent the primary detection signals identified by Mandiant during incident response investigations.
4. Authentication Infrastructure Asset Inventory Verify complete inventory of authentication gateways, SSO providers, and identity infrastructure. Assets not in inventory cannot be patched or monitored.
Structural (90-Day Transformation)
1. Event-Driven Session Management Implement automated session invalidation triggers for security events: vulnerability patching of authentication systems, password resets, MFA changes, suspicious authentication patterns. Session lifecycle must respond to security state changes.
2. EPSS-Based Prioritization Integrate EPSS scores into vulnerability management workflow alongside CVSS severity. Vulnerabilities with EPSS scores above 0.1, or with KEV catalog inclusion, warrant accelerated remediation procedures. FIRST.org's published model data demonstrates that EPSS-informed prioritization achieves substantially better efficiency against the exploited vulnerability population than severity-only approaches.
3. Identity Lifecycle Enforcement Establish maximum session duration policies independent of application defaults. Force re-authentication at defined intervals. Implement session token rotation for long-lived sessions. Treat authentication artifacts as security-sensitive objects requiring active lifecycle management, not passive byproducts of the login process.
4. Authentication Infrastructure Monitoring Deploy dedicated monitoring for authentication systems separate from application monitoring. Track session issuance patterns, geographic distribution of session usage, concurrent session counts per user, and session token reuse patterns across accounts.
Sector-Specific Implications
Critical Infrastructure NetScaler appliances commonly provide remote access to operational technology networks and industrial control systems. Session hijacking enables IT-to-OT pivot without exploiting air-gap controls. Organizations operating OT environments face elevated risk from authentication gateway compromise.
Federal Agencies BOD 22-01 mandates 15-day remediation for KEV vulnerabilities on internet-facing systems. CVE-2023-4966 entered KEV on October 18, creating a November 2 deadline. Agencies that patched without session invalidation remained vulnerable through hijacked tokens despite technically meeting compliance requirements on patch deployment timelines.
Financial Services Session hijacking bypasses transaction authentication controls. An attacker using a valid session token inherits the user's authorization level for financial transactions. MFA provides no protection against attacks that operate using post-authentication session artifacts.
The Operator Checklist
If You Run a Security Program, Check This Now:
☐ Do you maintain complete inventory of authentication infrastructure (SSO providers, VPN gateways, identity providers, authentication appliances)?
☐ Does your vulnerability remediation process include session invalidation as a mandatory step for authentication system patches not optional guidance?
☐ Do you monitor for session tokens used from multiple IP addresses simultaneously, or for mismatched client and source IP fields in authentication gateway logs?
☐ Are KEV-listed vulnerabilities automatically escalated to emergency remediation procedures with defined SLA clocks?
☐ Do you incorporate EPSS scores into prioritization decisions alongside CVSS severity?
☐ Can you detect authentication to your systems without a corresponding authentication event indicating a compromised session token in use?
☐ Do you enforce maximum session duration independent of application defaults?
☐ Does your password reset process invalidate all active sessions for affected accounts?
☐ Do you have network-level visibility into authentication gateway traffic separate from appliance-resident logs?
☐ Can you identify all users with active sessions to critical systems within 15 minutes?
Critical Takeaway: Vulnerability management measures patch deployment. Identity governance measures authentication artifact lifecycle. CitrixBleed proved these represent distinct security operations. Organizations that patched without invalidating sessions eliminated the vulnerability while maintaining attacker access through hijacked tokens.
The control failure was not in patching speed. It was in understanding what patching accomplishes and what it does not.
About This Report
Reading Time: Approximately 15 minutes
Attribution Note
Article Methodology: This analysis synthesizes threat intelligence from incident response findings, vendor security advisories, federal vulnerability catalogs, and exploitation tracking systems. All claims regarding exploitation timelines, threat actor scope, and technical exploit mechanisms are sourced from publicly available security research and government disclosures. Nation-state APT group attribution references Mandiant's public reporting of multiple distinct tracked clusters during the CitrixBleed zero-day period; specific internal threat cluster designations from Mandiant's non-public intelligence reporting are not cited as public sources. EPSS efficiency calculations reference published FIRST.org model data. Boeing attribution derives from the CISA/FBI Joint Advisory AA23-325A. ICBC attribution derives from researcher analysis subsequently corroborated by the US Treasury.
Author Information
Timur Mehmet | Founder & Lead Editor
Timur is a veteran Information Security professional with a career spanning over three decades. Since the 1990s, he has led security initiatives across high-stakes sectors, including Finance, Telecommunications, Media, and Energy. Professional qualifications over the years have included CISSP, ISO27000 Auditor, ITIL and technologies such as Networking, Operating Systems, PKI, Firewalls. For more information including independent citations and credentials, visit our About page.
Contact:
Editorial Standards
This article adheres to Hackerstorm.com's commitment to accuracy, independence, and transparency:
- Fact-Checking: All statistics and claims are verified against primary sources and authoritative reports
- Source Transparency: Original research sources and citations are provided in the References section below
- No Conflicts of Interest: This analysis is independent and not sponsored by any vendor or organization
- Corrections Policy: We correct errors promptly and transparently. Report inaccuracies to
This email address is being protected from spambots. You need JavaScript enabled to view it.
Editorial Policy: Ethics, Non-Bias, Fact Checking and Corrections
Learn More: About Hackerstorm.com | FAQs
Source Transparency
Current Threat Intelligence (April 2026)
• CISA Known Exploited Vulnerabilities Catalog U.S. Cybersecurity and Infrastructure Security Agency https://www.cisa.gov/known-exploited-vulnerabilities-catalog
• CISA Adds Eight Known Exploited Vulnerabilities to Catalog (April 20, 2026) U.S. Cybersecurity and Infrastructure Security Agency https://www.cisa.gov/news-events/alerts/2026/04/20/cisa-adds-eight-known-exploited-vulnerabilities-catalog
• CISA Adds CVE-2026-35616 – Fortinet FortiClient EMS (April 6, 2026) U.S. Cybersecurity and Infrastructure Security Agency https://www.cisa.gov/news-events/alerts/2026/04/06/cisa-adds-one-known-exploited-vulnerability-catalog
• BlueHammer, RedSun, and UnDefend: Three Windows Defender Zero-Days Exploited in the Wild SOCRadar Cyber Intelligence https://socradar.io/blog/bluehammer-redsun-undefend-windows-defender-0days/
• BlueHammer & RedSun: Windows Defender CVE-2026-33825 Zero-Day Vulnerability Explained Picus Security https://www.picussecurity.com/resource/blog/bluehammer-redsun-windows-defender-cve-2026-33825-zero-day-vulnerability-explained
• Three Microsoft Defender Zero-Days Actively Exploited; Two Still Unpatched The Hacker News https://thehackernews.com/2026/04/three-microsoft-defender-zero-days.html
• Microsoft April 2026 Patch Tuesday Fixes Two Zero Days, Including BlueHammer Field Effect https://fieldeffect.com/blog/microsoft-april-2026-patch-tuesday-bluehammer
CitrixBleed (CVE-2023-4966) Primary Sources
• Investigation of Session Hijacking via Citrix NetScaler ADC and Gateway Vulnerability (CVE-2023-4966) Google Cloud Threat Intelligence (Mandiant) https://cloud.google.com/blog/topics/threat-intelligence/session-hijacking-citrix-cve-2023-4966/ Primary source for zero-day exploitation timeline, session hijacking mechanics, detection methodology, and post-exploitation activity across multiple incident response engagements.
• Guidance for Addressing Citrix NetScaler ADC and Gateway Vulnerability CVE-2023-4966 U.S. Cybersecurity and Infrastructure Security Agency https://www.cisa.gov/guidance-addressing-citrix-netscaler-adc-and-gateway-vulnerability-cve-2023-4966-citrix-bleed
• #StopRansomware: LockBit 3.0 Ransomware Affiliates Exploit CVE-2023-4966 Citrix Bleed Vulnerability (AA23-325A) CISA / FBI / ACSC Joint Advisory https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-325a Primary source for Boeing confirmation and LockBit TTPs as voluntarily shared by Boeing Distribution Inc.
• NetScaler Security Bulletin and Investigation Recommendations for CVE-2023-4966 Cloud Software Group / NetScaler https://www.netscaler.com/blog/news/cve-2023-4966-critical-security-update-now-available-for-netscaler-adc-and-netscaler-gateway/ Vendor-issued session kill commands and official remediation guidance.
• Exploitation of Citrix NetScaler Information Disclosure Vulnerability (CVE-2023-4966) Rapid7 https://www.rapid7.com/blog/post/2023/10/25/etr-cve-2023-4966-exploitation-of-citrix-netscaler-information-disclosure-vulnerability/ Public proof-of-concept release October 25, 2023; technical exploitation analysis.
• 12 Questions and Answers About Citrix Bleed (CVE-2023-4966) Security Scientist https://www.securityscientist.net/blog/12-questions-and-answers-about-citrix-bleed-cve-2023-4966-2/
Vulnerability Prioritization & Risk Assessment
• Exploit Prediction Scoring System (EPSS) Model FIRST.org https://www.first.org/epss/model Source for CVSS vs EPSS efficiency statistics: CVSS 7+ strategy - 57.4% effort, 3.96% efficiency; EPSS 0.1+ strategy — 2.7% effort, 65.2% efficiency. Data as of October 1, 2023 NVD baseline.
Regulatory & Compliance Framework
• Binding Operational Directive 22-01: Reducing the Significant Risk of Known Exploited Vulnerabilities U.S. Cybersecurity and Infrastructure Security Agency https://www.cisa.gov/news-events/directives/binding-operational-directive-22-01
• National Vulnerability Database (NVD) National Institute of Standards and Technology (NIST) https://nvd.nist.gov/
