Critical Threat Intelligence & Advisory Summaries
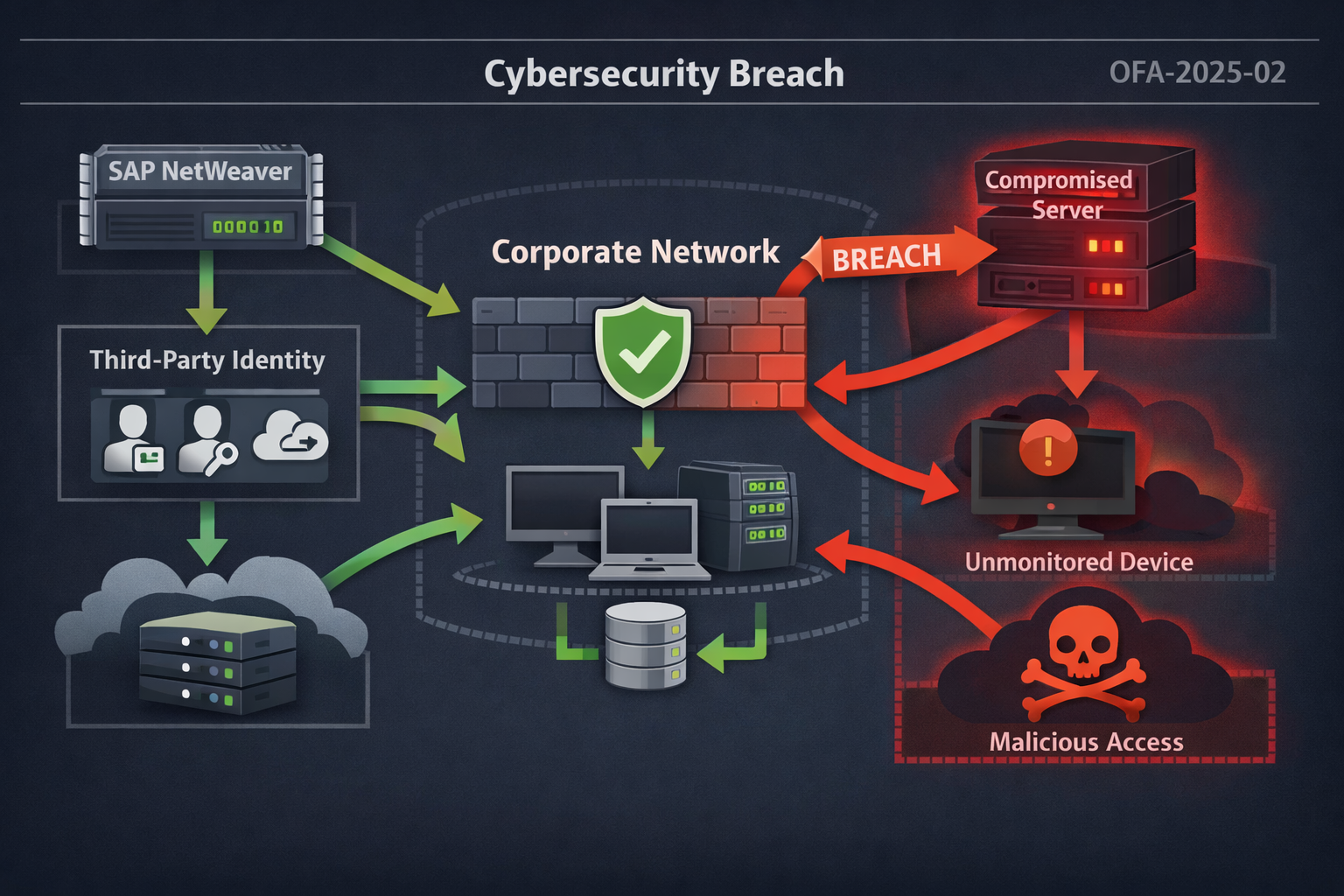
JLR breach analysis highlighting third-party identity exposure, KEV prioritization gaps, and lessons for operational threat intelligence teams.
Operational threat intelligence enables security teams to prioritize real-world risks through detection-focused monitoring and actionable insight. This guide addresses detection challenges, attack chain visibility, and defensive strategies for SOCs confronting identity-based threats, insider risk, and AI-enabled cyber campaigns.
AI-driven impersonation attacks including deepfake video fraud, voice cloning scams, and synthetic job applicants are redefining enterprise cyber risk. This guide explains the threat landscape and how SOC teams can detect and mitigate AI-enabled identity attacks.
KnowBe4 detected a suspected North Korean IT worker within 25 minutes of onboarding, exposing operational risks from AI-generated resumes, deepfake interviews, and synthetic identities. Security teams should focus on onboarding monitoring, least-privilege access, and early behavioral detection to prevent persistent insider threats.
WASHINGTON, D.C. - February 16, 2026 - The Cybersecurity and Infrastructure Security Agency (CISA) has issued a mandatory federal directive requiring the remediation of six Microsoft zero-day vulnerabilities by March 3. Linked to active exploitation by nation-state actors including Salt Typhoon, these flaws represent a critical escalation in the 2026 vulnerability landscape.